We tend to obsess over a particular three-letter acronym - OSS - but this week the whole world is fired up over one that is new for many - NFT. Non-fungible tokens (essentially cryptographically variable assets on a blockchain) are having their coming out party this week. Christie's sold some of Beeple's (aka Mike Winkelmann) artwork for $69 million to an unknown buyer going by the name Metakovan. Another platform, NBA Top Shots, is having a similar coming out party with mostly cheaper (although, not always) NFT digital video trading cards of your favorite basketball stars that are officially sanctioned by the NBA. One collector/investor claims to have spent $175K last fall on a collection worth $20M today.
The big news in the public open source markets is the acquisition of 17-year-old data integration firm Talend by private equity giant Thoma Bravo for $2.4 billion. While not the largest transaction within the context of what we are experiencing these last few years in enterprise software, it does signify the growing importance of open source as a core strategy for both strategic and financial acquirers. The Talend acquisition represented a 29% premium to the March 9th close price and a good outcome for shareholders who rode the wave of both open source and data analytics revolutions. While Talend may not be as well known as Alteryx, Informatica, FiveTran, Matillion, or Mulesoft (part of Salesforce) the transaction could facilitate future consolidation with additional products from companies around the ecosystem in a similar vein to other recent private equity rollups.
In this edition (and continuing our thread on OSS security), we also spent time with Aaron Bray, the CEO and co-founder of Phylum, who is developing DevSecOps tooling to help developers identify and mitigate risks stemming from the open source ecosystem. Aaron discusses the inherent risks in using OSS technology as well as the growing enterprise interest in the segment.
Private Markets
Aqua Security, a Burlington, Mass. and Ramat Gan, Israel-based cloud native security company, raised $135 million in Series E funding, valuing it over $1 billion. Ion Crossover Partners led the round and was joined by investors including M12, Lightspeed Venture Partners, Insight Partners, TLV Partners, Greenspring Associates, and Acrew Capital.
Snyk, a Boston-based cloud native application security company, raised $175 million in Series E funding with $125 million raised via secondary transactions. The round, led by Accel and Tiger Global, values the business at $4.7 billion.
Privacera, a Fremont, Calif.-based cloud data governance and security company, raised $50 million. Insight Partners led the round and was joined by investors including Sapphire Ventures, Battery Ventures, Accel, Cervin, and Point 72.
Yugabyte, the high-performance distributed SQL database for global internet-scale apps, announced a $48M Series C led by Lightspeed Venture Partners.
Tetrate, a San Francisco-based cloud application networking company, raised $40 million in Series B funding. Sapphire Ventures led the round and was joined by investors including Scale Venture Partners and NTTVC.
Hugging Face, a New York-based natural language processing technology company, raised $40 million in Series B funding. Addition led the round and was joined by investors including Lux Capital, A.Capital, and Betaworks.
Airbyte, provider of an open-source data integration platform, announced a $5.2M seed led by Accel.
Public Markets
To track the performance of COSS companies, we’ve created an equal-weighted index comprised of public names including: MongoDB, Elastic, Talend, Cloudera, Rapid7, Fastly and Jfrog.
Over the last year, the COSS Index significantly outperformed the benchmarks:
COSS Index +148%
NASDAQ +44%
S&P 500 +59%
Over the last three years, the COSS Index continues to outperform:
COSS Index +81%
NASDAQ +77%
S&P 500 +42%
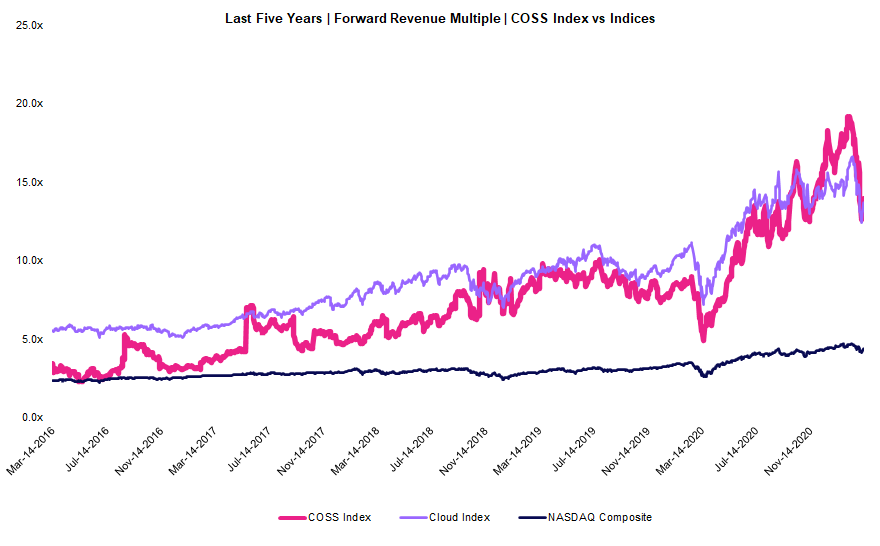
COSS companies sold off over the last two weeks nearly eliminating their recent premium above Emerging Cloud companies. However, all three indices continue to trade higher than their five-year average (although that trend has moderated in recent weeks and we’ll continue to watch closely).
COSS Index: Current Multiple 13.8x | Five-Year Mean: 7.3x
Emerging Cloud Index: Current Multiple 13.5x | Five-Year Mean: 8.8x
NASDAQ Composite: Current Multiple 4.4x | Five-Year Mean: 3.1x
Interview with Aaron Bray, the co-founder and CEO of Phylum
What is your background and how did you come up with the idea to start Phylum?
[Aaron] My background, I started out in the federal space, spent a bunch of years working in government in various capacities, including with one of my co-founders, Louis Lang, who also spent a lot of time in that realm. That realm was where we first stumbled across this problem and how big of an issue it was. At the time, of course, the federal government who has very markedly different security concerns than most of the rest of the world in terms of the things they're really concerned about and all of that, it was great that they were super concerned with this. But then if we fast forward a few years, there's just been such a great shift in the landscape of how open source is used, how it's consumed, who's involved with it, and more importantly, the number and type of issues that have really risen up over the last two or three years. We started to see so many more open source software supply chain borne attacks, where people have added malware or back doors upstream for major projects, and of course, Solarwinds is front of mind, but even over the last few months, we've seen things like Twilio’s SDK getting backdoored. Even in the last couple weeks, we've had some pretty major fundamental design flaws with how package managers work with these dependency confusion and repo jacking type of issues. So, just keeping an eye on those things after becoming aware of the issue to begin with, we decided to launch Phylum, because we just see this becoming more prevalent and larger over time.
Why start an open source company [Phylum] to address this?
[Aaron] Absolutely. We really saw this flaw as being largely unaddressed by current offerings in marketplace. There's a few that message in the direction of tackling it, but under the hood, most of them really rely on large teams of security engineers that they hire. We're getting to the point now where the trajectory of the open source ecosystem, how it's growing, how many dependencies per library you end up having, I think for JavaScript alone, it's somewhere in the neighborhood of 40 on average, it really just doesn't scale very well when you try and have people go in and audit all of these things. Even if you hire a lot of them, and even if you're smart about how you triage which things you look at, there's really no path to being proactive in preventing these issues from arising. So, we started with open source, and in the longterm, we also hope to grow into the closed source and proprietary side of things as well.
What is Phylum?
[Aaron] Really at its core, what we've done with Phylum is we've built a system that allows us to identify and triage major issues, and really fundamental risks in using third party and open source libraries in a fully automated way. And so, what this means really is we look at really all the domains of information that we can from source code, to package composition, to authors and their relationships, and their behavior, and all of the metadata that really surrounds packages from things like open issues on GitHub or GitLab, or other large centers of gravity in the open source ecosystem and beyond.
Snyk announced a large fund raise this week and has been drawing attention to the ecosystem, how does Phylum compare?
[Aaron] Great question. So really at a high level, I think we are asking a fundamentally different question than products like Snyk. Products like Snyk focus on a portion of the supply chain risk, with things like producing a software bill of materials, with looking at license issues, known vulnerabilities and known issues that are well distributed, well cataloged, and relatively easy to aggregate and reason about. What we really do is, we dig for those unknown risks that live in the supply chain. So, identifying in real time issues like malicious code, back doors, trojan packages, and other similar issues, are our bread and butter really. And also looking at things like the engineering risk that these packages bring to the table, so things like, doesn't have adequate test coverage, is it just an abandoned package that's unmaintained? I think this is a super critical issue, even in really critical infrastructure type spaces, where you have a lot of C code bases that contain maybe a lot of legacy libraries and things of that nature.
How are enterprise companies thinking about addressing vulnerabilities from an open source standpoint?
[Aaron] It has changed very dramatically over the last year. Just for clarification, we were founded in May of last year, and so just in that span of time, we have seen a pretty drastic shift in the landscape, both in terms of how the investor and enterprise communities are thinking about this, and really the type of questions that people are asking. If you look at what people were thinking about, even just a year ago, a lot of organizations are at the very beginning of their journey in terms of building a real robust AppSec program. A lot of them are thinking through what they need to compose, and what they need to put together, and what kind of questions they really need to ask in order to be effective with the dollars they're spending. These software bill of material and license issues are low hanging fruit that's been pretty well known and well studied over the last decade or more. But now we've got a new landscape of emerging threats that have really just come into focus in the last three to six months in a lot of ways, with more focus on actual malware being deployed with things like crypto miners. That sort of stuff has really, I think shifted the way that people are thinking about the space and the problem as a whole.
Given the large scale of the open source ecosystem, where do you focus?
[Aaron] I think in terms of this particular problem domain/problem space, it can even be a little bit market vertical specific, say for example, there are a lot of new mandates rolling out from the federal side that are focused on more granular supply chain checks and more granular software supply chain security, but there was even trickle over in some ways to other segments as well. I think that very broadly, a large part of this open source landscape is really fundamentally undefended. And so by that I mean, we saw just a couple of weeks ago a bunch of incidents where a security researcher was able to claim a few hundred thousand dollars plus bug bounties from Apple and Microsoft, and a bunch of other very large companies, by way of this fundamental design flaw in the package manager ecosystem called dependency confusion. Effectively, what he was able to do is go identify packages that were internal to these organizations in their external repositories, and he was able to go and bump the version numbers of those packages until he started getting downloads, and was able to then execute code inside of these organizations, and on their networks, and on their developer workstations, and on their CI infrastructure. The broader point there is not so much this particular design flaw, but this is endemic of a bigger problem, and it's really been unexplored for a long time. What we've seen through Solarwinds over the last two months could give attackers enough leverage to be able to execute a variant of Solarwinds on any organization they wanted.
What is the enterprise rationale for implementing the Phylum solution?
[Aaron] Of course, there's the traditional compliance concerns around things like licenses, and whether or not they're commercially viable, and more broadly, whether they could cause potential IP issues down the line if they incorporate them. But there's also that other set of concerns around the security angle, of course, vulnerabilities are part of that, but also getting a good understanding of the health and how well maintained a lot of these packages are. There's a long hidden tail with the maintenance side of some of these libraries. If you end up with one that's been abandoned or was poorly maintained, or has foundational security or design flaws, then that can create a lot of issues, certainly. We as a company are very focused on trying to help police those ecosystems in an automated fashion. There is at least a little bit of cursory work, I think that can be done outside of purchasing products to try and get a handle on, at least a base level of these issues. Unfortunately, we're getting very granular and in the weeds is very difficult just by virtue of the fact that the length of these graphs is so large. I mean just as an example, one of the first packages we took a look at the very beginning was React. It's very popular library developed by Facebook, it's used by tons of organizations, large and small all over the world. We found it has something like three first level dependencies, but if you follow the graph all the way out, you end up with something like 7,000 possible packages that could get pulled in by installing React, and maybe in even more insidious part of this problem is you don't get all 7,000 of those packages at once or in one location, you get some subset of that 7,000.
Extra
Equinix METAL is doing things | Specialized HW and Why Open Source Will Drive Adoption | Replay the First Technical User Conference